Inspect Incoming Call Data Logs – 111.90.150.2044, 111.90.150.204l, 111.90.150.2404, 111.90.150.282, 111.90.150.284, 111.90.150.288, 111.90.150.294, 111.90.150.2p4, 111.90.150.504, 111.90.1502
The incoming call logs for addresses in the 111.90.150.x range present a mixed signal set. Preliminary attention should focus on timing, frequency, and interarrival patterns to distinguish routine traffic from anomalies. Variants in endpoints (e.g., 2044, 2404, 282, 284, 288, 294, 504) suggest potential aliasing or mis-typed identifiers, warranting validation of provenance and source signals. A disciplined, automated approach will be required to separate reproducible baselines from irregular bursts and to establish a defensible risk posture. The implications of early findings will shape subsequent verification steps.
What Incoming Call Logs Tell Us About Caller Intent
Incoming call logs offer a structured record of caller behavior that can illuminate intent with minimal interpretive bias. The analysis focuses on timing, frequency, and response patterns to infer caller intent. Data interpretation emphasizes consistent metrics over anecdote, reducing noise. Evidence-based conclusions emerge from cross-referencing call duration, origin, and interarrival intervals without presuming motive.
Spotting Patterns and Anomalies in 111.90.150.x Logs
Pattern and anomaly detection in 111.90.150.x logs centers on objective examination of timing, frequency, and source characteristics to identify deviations from established baselines. Analysts map caller patterns across intervals, compare against normal traffic, and flag irregular bursts or unfamiliar origins.
Evidence-based insights emerge from synchronized metrics, highlighting anomalies where legitimacy and risk diverge, guiding informed, freedom-preferring decision-making.
Practical Steps to Verify Legitimacy and Reduce Risk
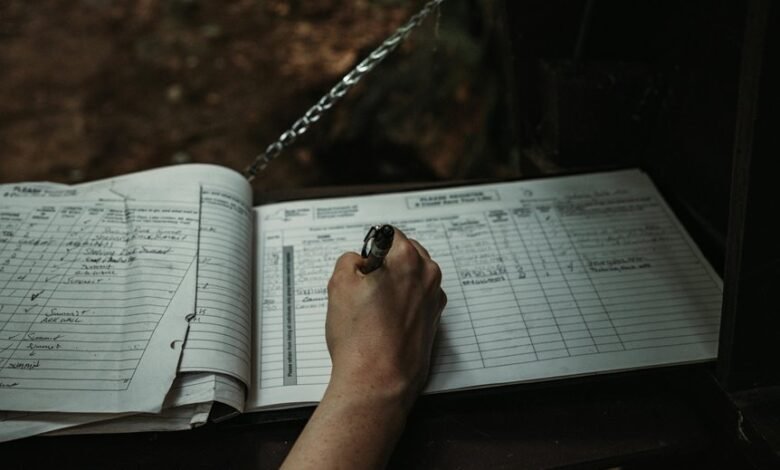
To verify legitimacy and reduce risk in incoming call data logs, practitioners implement a structured, evidence-based workflow that integrates timing analysis, caller origin assessment, and corroborating signals from auxiliary data sources.
The approach remains disciplined, avoiding unrelated topics and unrelated methods, focusing on verifiable indicators, cross-checks, and reproducible procedures to minimize exposure while preserving analytical freedom and operational clarity.
Common Pitfalls and Best Practices for Call Data Hygiene
Common pitfalls in call data hygiene often stem from incomplete data capture, inconsistent formats, and insufficient validation checks, which collectively undermine reliability and operational decisions.
The discussion emphasizes insightful hygiene through rigorous data reconciliation, standardized schemas, and explicit provenance.
Practitioners should implement automated validation, cross-source reconciliation, and continuous auditing to sustain data integrity, reduce anomalies, and support confident risk assessment and decision-making.
Conclusion
In sum, the incoming call logs from 111.90.150.x reveal a pattern of variable interarrival times and mixed source signals, suggesting mixed legitimacy and potential automated bursts. Consistent validation against baselines reduces false positives, while provenance tracking ensures reproducibility. An anticipated objection might claim the data volume is insufficient for firm risk judgments; however, cross-referenced timing, duration, and origin signals provide a defensible, evidence-based basis for risk-aware decisions and ongoing auditing.








