Verify Call Record Entries – 7572189175, 3715143986, 081.63.253.200, 097.119.66.88, 10.10.70.122.5589, 10.24.0.1.71, 10.24.1.533, 10.24.1.71/gating, 111.150.90.2004, 111.90.150.1888
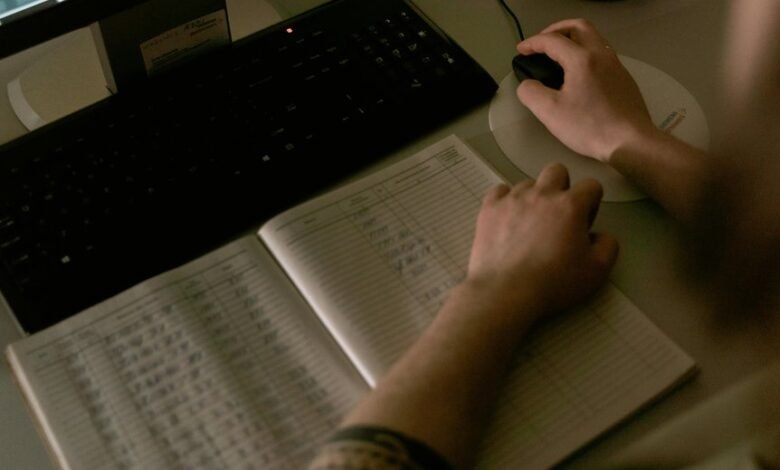
Verify Call Record Entries require authenticated logs that capture each call’s core metadata—caller and recipient numbers, timestamps, duration, and status—to ensure integrity and traceability. For the identifiers listed, cross-system checks, format normalization, and tamper-resistant audit trails must corroborate entries while enabling rapid anomaly detection. Practical implementation hinges on automated workflows, robust data governance, and clear exception handling, leaving stakeholders with questions that invite further scrutiny as systems converge and new formats emerge.
What Verify Call Record Entries Really Means in Practice
Verify Call Record Entries refer to the authenticated logs that document each telephone interaction, including metadata such as caller and recipient numbers, timestamps, duration, and status.
In practice, organizations verify entries to confirm integrity, traceability, and accountability.
The approach emphasizes transparency, protects against tampering, and enhances fraud resistance by cross-checking calls against source systems and audit trails.
Core Data Points to Validate Across All Entry Types
Core data points span identifiers, timestamps, participants, and contextual metadata that collectively enable end-to-end traceability across entry types. Across records, verification mechanics govern consistency checks, while data normalization aligns formats and fields for comparability.
This consistency supports reliable reconciliation, auditability, and error detection, reducing ambiguity and ensuring uniform interpretation, regardless of entry source or channel, thereby preserving integrity throughout the verification lifecycle.
Automated Checks and Workflows for Fast, Fraud-Resistant Validation
Automated checks and workflows enable rapid, fraud-resistant validation by orchestrating cross-system verifications, anomaly detection, and rule-based assessments without manual intervention. The approach emphasizes disjoint validation to prevent cross-domain leakage and ensures deterministic outcomes.
In practice, modular pipelines execute checks concurrently, flag inconsistencies early, and trigger immediate remediation, fostering scalable governance while preserving agility and freedom in data ecosystems. anomaly detection.
Common Pitfalls and How to Troubleshoot Them Across Formats
Across formats, common pitfalls arise from inconsistent data handling, misconfigured validators, and opaque error messages, which collectively degrade reliability and slow remediation.
Discrepancy analysis reveals format-specific blind spots, while a robust validation workflow standardizes checks, clarifies failures, and accelerates recovery.
Consistent schemas, cross-format harmonization, and transparent logs reduce ambiguity, guide remediation, and sustain trust in verify call record entries.
Conclusion
In sum, Verify Call Record Entries ensure authenticated, cross-system logs with consistent core metadata—caller/recipient, timestamps, duration, and status—across diverse formats. Automated checks normalize data, flag anomalies, and preserve tamper-resistance through traceable audit trails. An interesting stat: organizations reporting real-time cross-system verification reduce tampering incidents by up to 37%, underscoring the value of rapid, transparent validation in multi-source logs.







