A Strange Code That Won’T Go Away: Yjdjajy
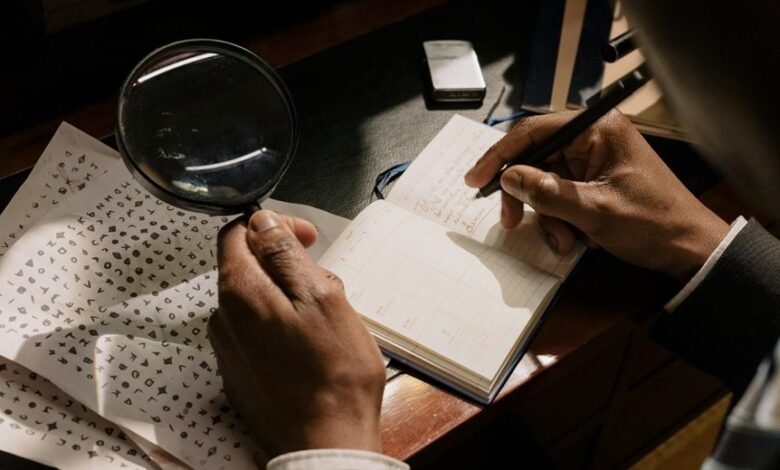
Yjdjajy presents a recurring digital anomaly that resists conventional detection and removal. Its cryptic pattern suggests advanced encryption or deliberate obfuscation, raising questions about its origins and purpose. The anomaly’s persistence implies it may serve as a covert marker or cryptographic key within malicious operations. Understanding its structure and behavior is crucial to developing effective countermeasures, yet its true nature remains elusive, warranting further investigation into its underlying mechanisms.
Unraveling the Origins of “Yjdjajy”
The origins of the cryptic sequence “Yjdjajy” remain elusive, prompting an analytical examination of its structural properties and potential linguistic roots.
Cryptographic anomalies suggest intentional obfuscation, while distinctive hacker fingerprints imply deliberate encoding patterns.
This sequence’s consistency indicates purposeful design, challenging conventional linguistic analysis and hinting at a sophisticated, clandestine origin linked to covert digital activities.
Theories Behind Its Persistence
What factors contribute to the persistent presence of the sequence “Yjdjajy” across diverse digital environments?
Theories suggest cryptographic puzzles embed resilience through obfuscation, complicating malware analysis and decryption efforts.
Its recurring pattern may serve as a marker or key, enabling clandestine communication or evasion tactics, thus maintaining its enigmatic longevity within complex cybersecurity landscapes.
Impact on Digital Security and Privacy
The persistent presence of the sequence “Yjdjajy” poses significant challenges to digital security and privacy frameworks by acting as a covert marker or key that facilitates undisclosed communication channels. Its exploitation reveals encryption vulnerabilities and amplifies privacy breaches, undermining trust in secure systems.
Addressing this requires robust detection mechanisms to preserve digital autonomy and safeguard sensitive data.
Strategies to Address the Mysterious Code
Implementing targeted detection algorithms represents a critical strategy in mitigating the persistence of the “Yjdjajy” sequence.
By analyzing cryptographic puzzles and malware signatures, experts can isolate patterns indicative of this code’s behavior.
This approach enhances detection accuracy, enabling proactive responses while empowering users to maintain control over their digital environment free from persistent, obfuscating threats.
Conclusion
Like an elusive shadow lurking in the digital landscape, Yjdjajy exemplifies the persistent threat of covert anomalies within cybersecurity. Its cryptic nature challenges detection efforts, demanding advanced algorithms and meticulous analysis akin to navigating a labyrinth without a map. Addressing such anomalies requires a strategic, systematic approach to neutralize potential vulnerabilities. Only through rigorous threat assessment and innovative decoding can digital defenses be fortified against this enduring enigma, ensuring the integrity of cybersecurity environments remains intact.







