Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account & Network Integrity Inspection integrates governance across identities, devices, and data flows to enable continuous auditing and rapid collaboration. By correlating signals from users and networks, it supports transparent controls, clear playbooks, and accountable data lineage. Anomalies trigger proactive risk management and measured responses, while trusted networks sustain resilience. This foundational approach invites further examination of thresholds, tooling, and governance models to determine how such practices scale in heterogeneous environments.
What Is Account & Network Integrity Inspection and Why It Matters
Account and Network Integrity Inspection is a systematic process used to verify that digital accounts and the underlying networks remain secure, unaltered, and trustworthy.
The practice supports data governance objectives by clarifying responsibilities, controls, and accountability.
It enables collaborative risk assessment and continuous improvement, while Trust analytics illuminate patterns, anomalies, and resilience across systems, guiding proactive governance without compromising freedom or privacy.
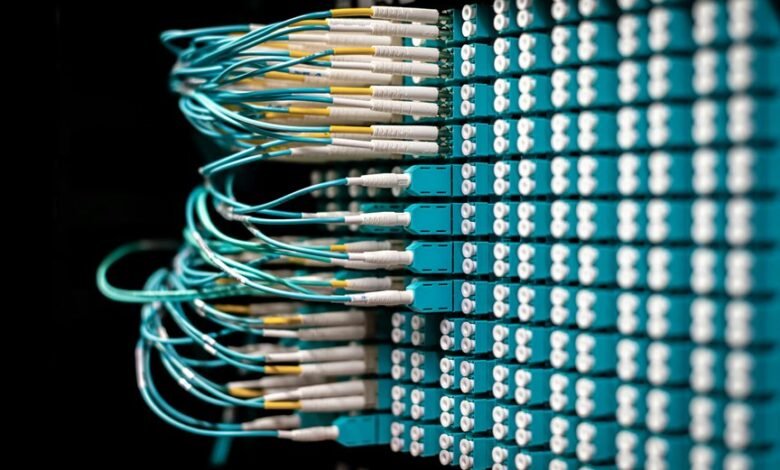
How to Monitor Integrity Across Users, Devices, and Data Flows
Effective monitoring of integrity across users, devices, and data flows requires a structured, evidence-based approach that correlates identity, endpoints, and data movement.
The analysis emphasizes monitoring integrity through cross domain visibility, continuous auditing, and governance practices, facilitating anomaly signals detection.
Collaborative teams establish rapid response protocols, aligning trusted networks and policies to sustain resilience, ensure accountability, and drive proactive risk management.
Detecting Anomalies: Signals, Thresholds, and Rapid Response Playbooks
Detecting anomalies hinges on translating disparate signals into coherent, actionable indicators. The analysis aggregates anomaly signals from multiple sources, establishing rapid response thresholds for monitoring that balance false positives with timely intervention. Collaborative teams define playbook automation to expedite containment, investigation, and recovery. Clear, repeatable criteria ensure consistent decisioning, enabling proactive defense while preserving user autonomy and system resilience.
Tools, Governance, and Best Practices for Trusted Networks
Tools, governance frameworks, and best practices underpin the maintenance of trusted networks by translating anomaly insights into repeatable, auditable actions.
The discussion examines how account governance, network monitoring, security architecture, and data lineage integrate to sustain integrity, enable collaboration, and empower freedom.
A meticulous, analytical approach emphasizes transparent policies, verifiable controls, and continuous improvement across heterogeneous environments.
Conclusion
The analysis demonstrates that account and network integrity inspection, by integrating signals from users, devices, and data flows, yields a cohesive, auditable security posture. When governance, playbooks, and trusted networks align, anomalies are detected with precision and addressed collaboratively across teams. The approach scales across heterogeneous environments, delivering continuous assurance. In effect, it elevates resilience to astronomical levels, ensuring transparency, accountability, and proactive risk management through meticulous, data-driven collaboration.







